Combining pen testing & vulnerability management
You know what a pen test is, but why do you need it?
Businesses are digitizing at a rapid pace, and most organizations lack the skills and expertise needed to create (and maintain) an effective cyber defense. Not only are the number of threats increasing, but also the number and stringency of regulatory demands. Cyber security platforms and products are a must, but are they smart enough to find what a cybercriminal can find?
The answer is no. A person is still needed to proactively find vulnerabilities that only the human mind can discover.
How do penetration testing & vulnerability management differ?
In simple terms, penetration testing is usually focused on a limited number of critical systems identifying complex, context-specific vulnerabilities. As penetration testing is a manual process carried out by experts, it’s both time consuming and costly. Vulnerability management, on the other hand, is an automated and continuous process that analyses your IT infrastructure to find vulnerabilities, with emphasis on “automated and continuous.” It provides speed, efficiency, and a broad attack vector coverage.
Here’s a more detailed comparison:
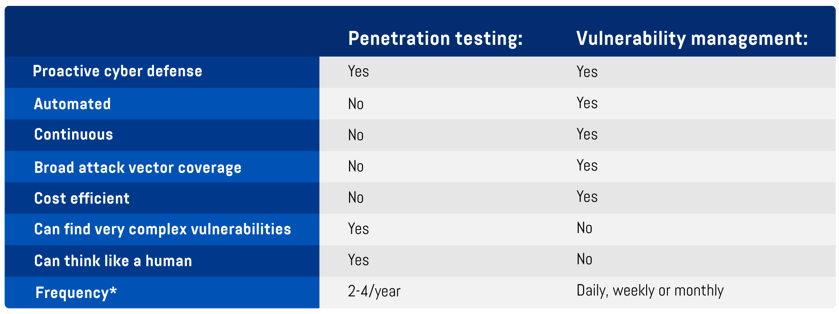
* The frequency is dependent on each organizations’ specific needs.
Vulnerability management is sometimes called automated penetration testing, as some tests are intrusive and will try to penetrate your systems, but also because vulnerability management will find many of the same vulnerabilities that a penetration tester will find. This means that enabling a vulnerability management solution frees up the pen tester to focus on what’s business-critical.
A powerful combo, but start with vulnerability management
Combining penetration testing and vulnerability management ensures a solid security posture and is essential for most organizations. But where do you start?
The answer is to begin with vulnerability management, and here’s why:
Don’t spend time on the obvious
Vulnerability management will find all obvious vulnerabilities, saving your penetration testing consultant time that can be spent on complex, context-specific vulnerabilities.
Create a great baseline to work from
A solid foundation will remove distractions, enabling manual penetration testing to cut through the noise and bring greater value.
Focus on what’s business-critical
An automated and continuous vulnerability management program allows the penetration testing consultant to focus on finding vulnerabilities that would cause the most damage to your organization.
Penetration testing is important
Remember, penetration testing is important. It excels in areas where real-world attack complexity and strategic human judgment are required, and it provides a clear picture of what an attacker could actually do if they were to breach your defenses. In short, it goes beyond finding vulnerabilities.
Conclusion: important practices in a modern proactive cyber defensePenetration testing and vulnerability management are two cyber security practices that are required for most organizations. They form a perfect combination. Remember to get your vulnerability management process in place before you start your penetration test. In this digital age, the question isn’t “Why should I implement vulnerability management and/or pen testing?” — it’s “Can I afford not to?” |

Jan Willem Plokkaar
Sales Director Benelux
Jan Willem has over 10 years' experience within cyber security. His former roles include sales and business development at companies like Canon and KPM. Currently, he works with organizations to reduce their risk posture and advises them on meeting security challenges.




